--> A Brute Force Attack is a method used by hackers to get access to a web server or web application by trying multiple combinations of usernames and passwords until the hacker is able to get into the application.
--> F5 ASM is able to detect and prevent brute force attacks by tracking the number of failed login attempts.
--> In order to track the number of failed login attempts by the users, The ASM needs to know the login page of the web application/web page.
--> ASM can detect the login pages automatically or we can manually add the login page on the security policy where you want to protect the web application from brute force attacks.
--> ASM Prevents brute force attacks by using two methods:
i) Session-Based Prevention :
--> Checks for the number of failed login attempts per-session cookie.
--> If the number of failed login attempts are more than the value configured under brute force protection then the ASM is going to generate the violation as " Brute Force: Maximum login attempts are exceeded violation".
--> If the security policy is set to blocking mode then the ASM is going to block the requests originating from the IP address.
ii) Dynamic Prevention:
--> Checks for the number of failed login attempts per login page.
--> Identifies and prevents brute force attacks based on a statistical analysis of the traffic.
--> ASM is going to block the request if the number of failed login attempts on the login page is more than the normal login attempts.
Steps to Configure Brute Force Protection:
1) Configure Login Page:
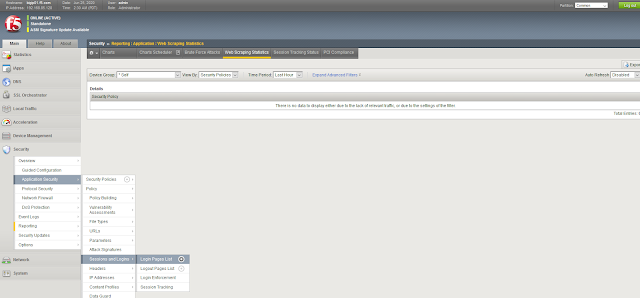
--> Navigate to Security > Application Security > Sessions and Logins under your selected security policy.
2) Configure Brute Force Protection:
--> Navigate to Security > Application Security > Anomaly Detection > Brute Force Attack Prevention.
--> We can detect the failed login attempts based upon following in Brute Force Protection Configuration:
i) Based upon Username ( Counts the number of failed login attempts per username)
ii) Based upon Device ID ( Counts the number of failed login attempts per Device ID)
iii) Based upon IP address (Counts the number of failed login attempts per IP address)
--> Either we can configure all the settings or anyone as per the requirement.
--> For each criteria we have the action( What to do when the number of failed login attempts are more than the configured value). We can block the requests or generate an alarm.
--> Distributed Brute Force Protection is used when there is a brute force that is happening from multiple IP addresses instead of one IP address.
--> ASM is going to check number of failed login attempts per login page in Distributed Brute Force Protection.
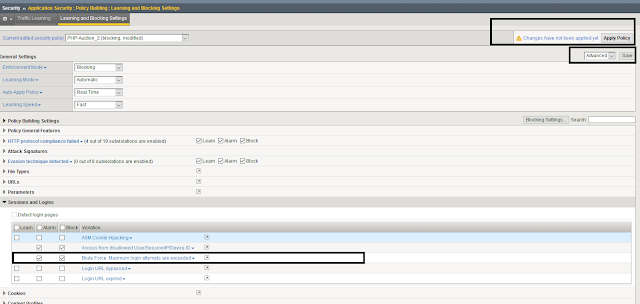
3) Enable Brute Force Protection Signature under Learning and Blocking Settings:
You have successfully enabled Brute Force Protection on the security policy of ASM.
Reference: F5.com,
Md.Kareemoddin,
CCIE # 54759, F5-CTS











0 comments:
Post a Comment