DNSSEC
--> DNS is the main component of Internet Communication.
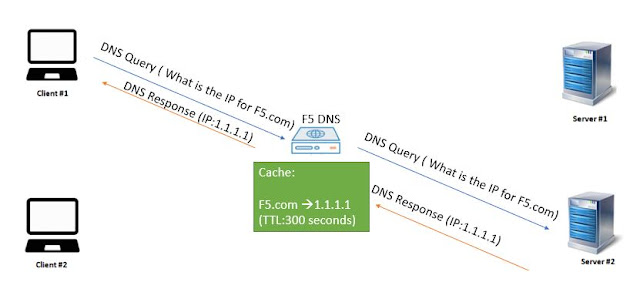
--> Basically Users use FQDN to communicate with any resource/server that is present over the Internet.
--> However the Machine/System used by user only understands the IP address, Here comes the DNS into the rescue which takes the FQDN and converts it into the IP address.
--> The Security was not taken into consideration when the DNS was developed by the developers and there is no way to identify the response which is coming from the DNS Server is accurate and correct.
--> DNSSEC is a security extension to the actual DNS Protocol.
--> DNSSEC uses digital signature records to provide security to the Zones ( In simple terms we can say Domains) present on the DNS Server.
--> There will be a digital signature present for each and every record created on the DNS Server.
--> Whenever user tries to resolve/find the IP address of any FQDN using DNS then the DNS Server is going to provide IP address as well the digital signature associated with it.
--> By verifying the digital signature which it got from the DNS Server, The machine can understand whether the provided IP address to the FQDN is accurate or not.
--> Digital Signature uses the concept of the private and public keys to verify the resource on the Internet. Each and every resource record which is created on the DNS Server is encrypted by using a Private key on the DNS server and can be verified by using the public key on the user machine.
--> A DNSSEC enabled Server needs to have a public and private key for each zone ( In simple terms understand kareemccie.com is a zone and www.kareemccie.com is a resource record).
--> When any user tries to find the IP address of www.kareemccie.com by sending the request to kareemccie.com DNS Server then the DNS Server is going to send a resource record by signing it with the private key.
--> The user then requires the public key to decrypt it and verify the information.
--> Now we understood that Digital Signatures are used to provide security to the DNS, We need to understand how this digital signature can be created and what are the extra records needed in the DNSSEC.
--> Below are the extra records that need to be created to implement DNSSEC:
1) RRSIG
--> Which is the digital signature that is sent along with each resource record ( Ex: Which is the IP address of the server) to the client.
--> Contains the private key in the RRSIG record.
--> Which can be decrypted by using DNSKEY
2) DNSKEY
--> DNSKEY is the public key that is present on the DNS Server.
--> Whenever the client receives the resource record along with RRSIG then in order to decrypt the RRSIG, The client requires the Public Key.
--> Using the DNSKEY the DNS Server is going to advertise the public key of the zone so that users can decrypt it.
3) DS
--> Contains the hash of a DNSKEY record.
--> Which needs to be provided to the Registrar to implement a chain of trust.
4) NSEC and NSEC3
--> If any DNS Resource record is not present on the DNS Server that can be informed to the client by using this record
Ref: F5.com,
Md.Kareemoddin,
CCIE #54759